It’s just awesome living next door to someone who doesn’t give a shit about other people.
My neighbor and his friends woke me up multiple times last night between 1:30am and 3am..
I just wanted to sleep, guess I’m not allowed according to him




It’s just awesome living next door to someone who doesn’t give a shit about other people.
My neighbor and his friends woke me up multiple times last night between 1:30am and 3am..
I just wanted to sleep, guess I’m not allowed according to him




So my neighbor had the tow truck driver park his car extremely close to my van, so close in fact that I can’t get in the back of it. I had plans yesterday to put some stuff in there, but I just couldn’t get in. I would have had to lie on the ground under my bumper to open the back of my van as it swings out and up, there’s just no way to open it with a car parked that close and there’s no reason to park that close either. Sure I could have pulled my van up to access the back, but why should I have to do that when there’s about 2-3 parking spaces of room behind his car?
New category for my little site here called “harassment” and here I’m going to document everything my neighbor has done and is doing to me and my family. We’ll start with this today, or this morning at 1:08am. I was woken up by by what sound like to me him and his friend slamming car doors, talking and actually what sounded to me like them stomping up the steps. I heard them walking actually, and talking right outside my window… fun-fun.
Since I have Counterize enabled on my blogs it’s always interesting to see what’s going on, and it’s kinda cool that the blogs will email me if there’s an error somewhere like someone trying to go somewhere on my site and not being able to access it…
Lately I’ve come across quite a few ‘hacker’ entries, and actually backtracked them to the originating server, and even went so far as to explore the stuff they’ve got in there, all of there hacking tools, like scanners etc. It’s really interesting because they like have their names right in there, or at least their aliases, they sign their programs and work, leave email addresses and IRC channel addresses to contact them with…
I also found it interesting that most of the hackers use PocketPCs to do this stuff…
Here’s a screencap from Counterize showing what I mean:
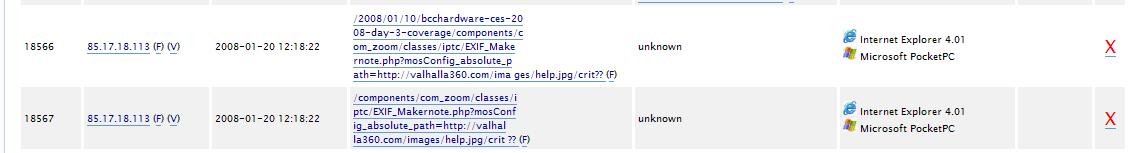
You can click the tiny one for it to open full screen to 1137×153 size…
anyway, I even went through their directories and downloaded the tools they use just to check them out and get some more info about them.. why, curiosity I guess…
as for Spammers, I was thinking, they are a real PITA, I get quite a bit of spam, thank God for Akismet really, but wouldn’t it be cool if those spammers would at least click on one of our ads? I mean they make use go through these junk messages/comments, couldn’t they at least make it worth our while to do so?
Back to the hackers… these guys are a trip, here’s an excerpt from their code:
# Release Name : XxX-SuperScan-XxX
#
# RFi Scanner Christmas Release ! 😀
#
# ————- [% Notes %] ————-
# This rfi scanner contains piece of code from; PitBull CreW, Mic22, Inphex.
# And also lets just say more version wil come 😛
#
# With this release you must be happy since its the best RFi Scanner around.
# And its even public, happy x-mas ! 😀
#
# You can also PM the bot with your scan, this is handy when you have loaded multiple scanners.
and here’s another that I found rather funny as well:
# Mafia_KB, i hope i pretty fucked up your sell
# asking 2000 fucking euros for a crappy scan ?
# this one is 1000 times better so i hope
# it affects your sell even more lol.
Oh well.. tis life I guess
350-018 is related to AES and EAP wireless protocols that maintain safe wireless access to devices across the branch networks. 70-297 is related to devising an Active Directory in addition to network infrastructure. 640-816 explains how VLANs produce logically detached networks and the requirement for routing between them. 156-215 generate rules and adapt a Security Policy’s properties. Candidates for 70-528 should have a functioning knowledge of Visual Studio 2005 and a solid knowledge of the latest features of ASP.NET 2.0.